The Challenge of IT and OT Asset Discovery
Introduction Why Complete Asset Inventory Is Essential The Ever-Expanding…
Brassard–Høyer–Tapp (BHT) Quantum Collision Algorithm and Post-Quantum Security
Introduction and Overview The BHT Algorithm: Quantum Collision-Finding How…
Adaptive Attacks: Learning to Evade Machine Learning-Based IDS
Introduction Understanding Intrusion Detection Systems Learning to Evade:…
Shor’s Algorithm: A Quantum Threat to Modern Cryptography
Introduction Background on RSA Encryption How RSA works (conceptually) Why…
Quantum Fourier Transform (QFT)
From Classical to Quantum: What QFT Does Why QFT Matters in Quantum…
Grover’s Algorithm and Its Impact on Cybersecurity
Introduction to Grover’s Algorithm Significance in Quantum Computing…
Hadamard Gate: The Gateway to Superposition
A Bit of History Definition and Matrix Hadamard on the Bloch Sphere…
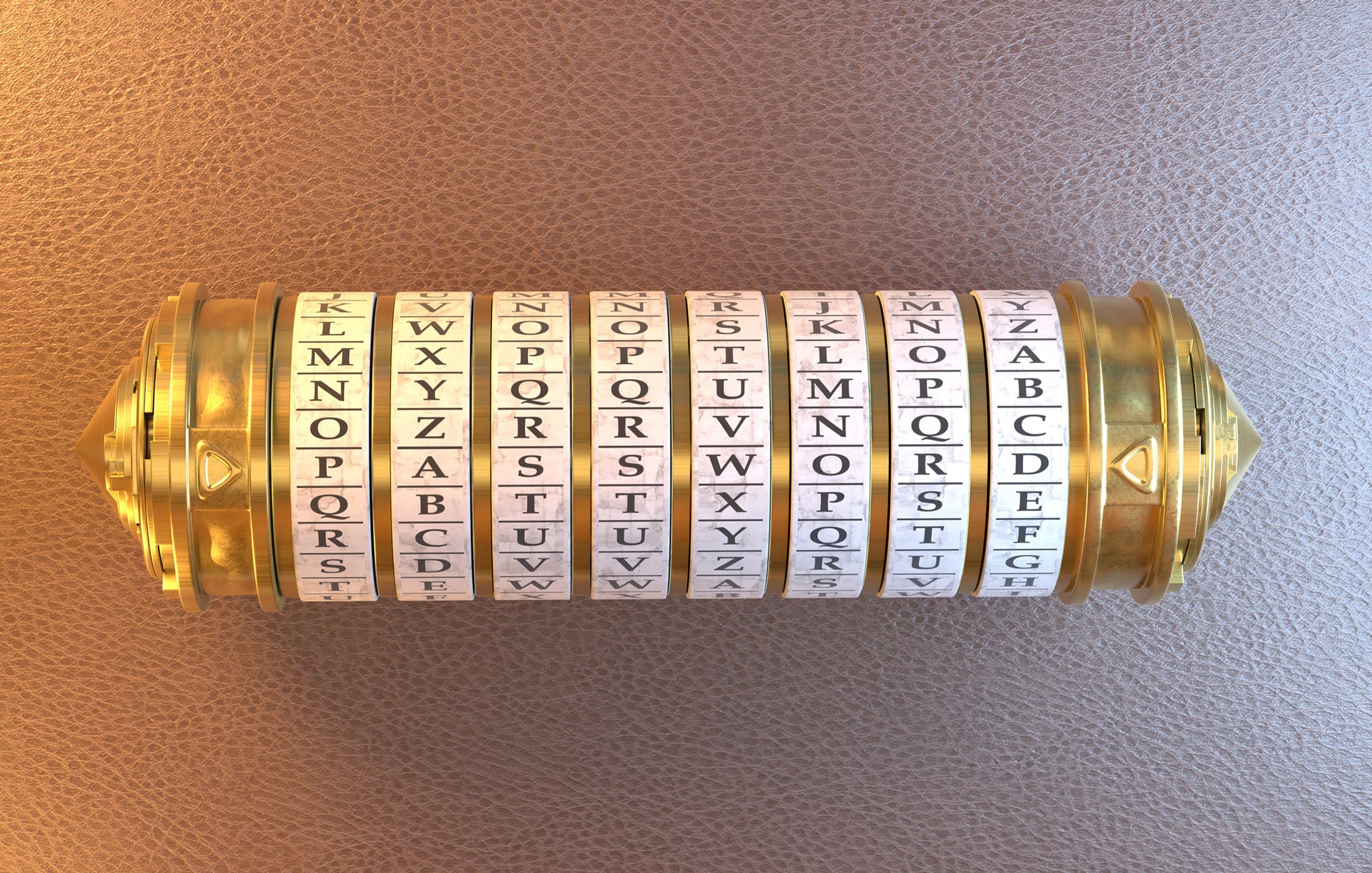
Quantum-Safe vs. Quantum-Secure Cryptography
In 2010, I was serving as an interim CISO for an investment bank. During that…
Quantum Superposition: How Qubits Live in Many States at Once
The Strangeness of Superposition: Schrödinger’s Cat and Other Paradoxes…
Colliding Waves: How Quantum Interference Powers Quantum Computing
What is Quantum Interference? From Wave Patterns to Computation A Tale of…