Quantum Readiness for Mission-Critical Communications (MCC)
Introduction to MCC and Quantum Threats Mission-critical communications…
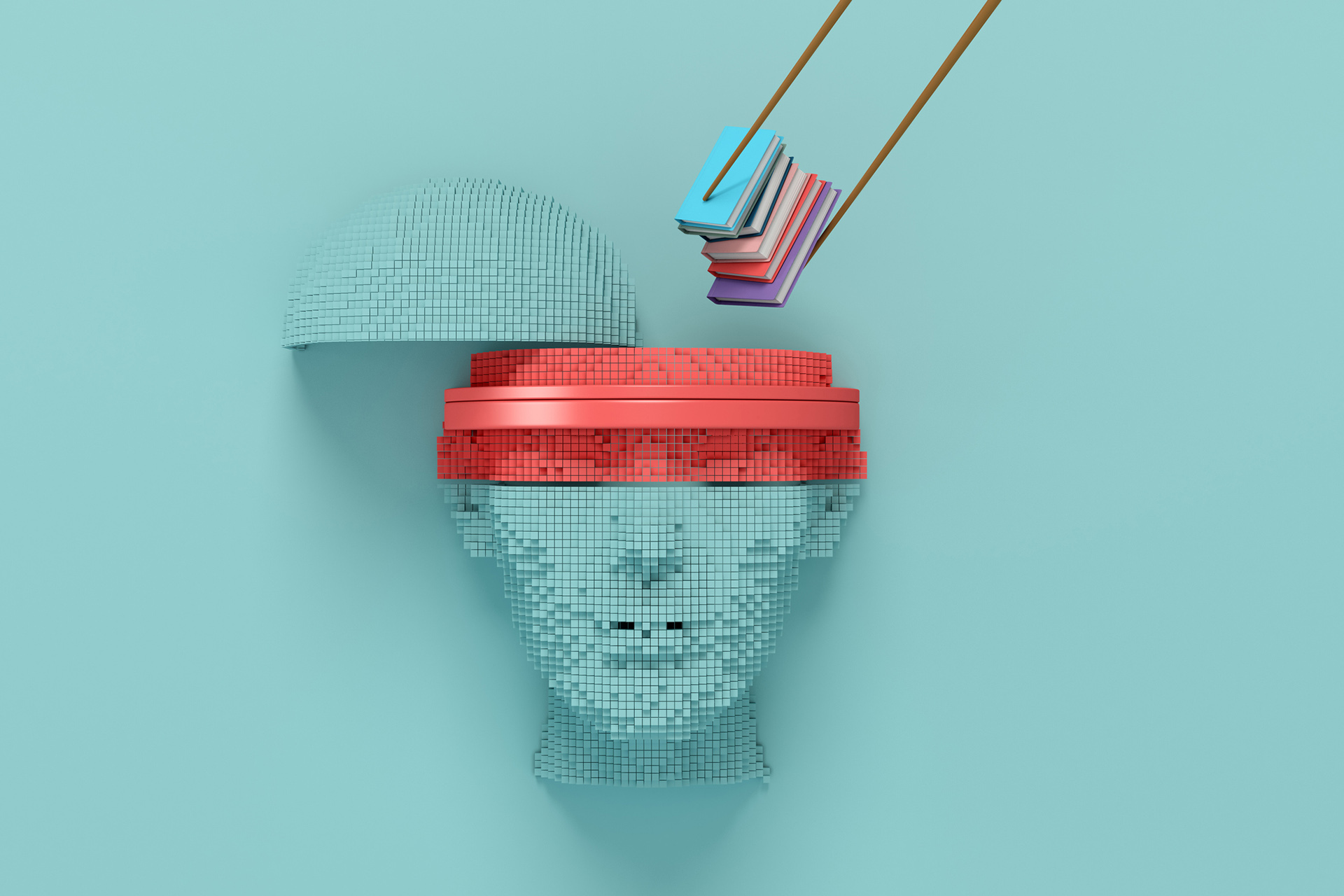
Understanding Data Poisoning: How It Compromises Machine Learning Models
Machine learning (ML) and artificial intelligence (AI) have rapidly…
Semantic Adversarial Attacks: When Meaning Gets Twisted
A particular subset of AI/ML adversarial attcks that often flies under the…
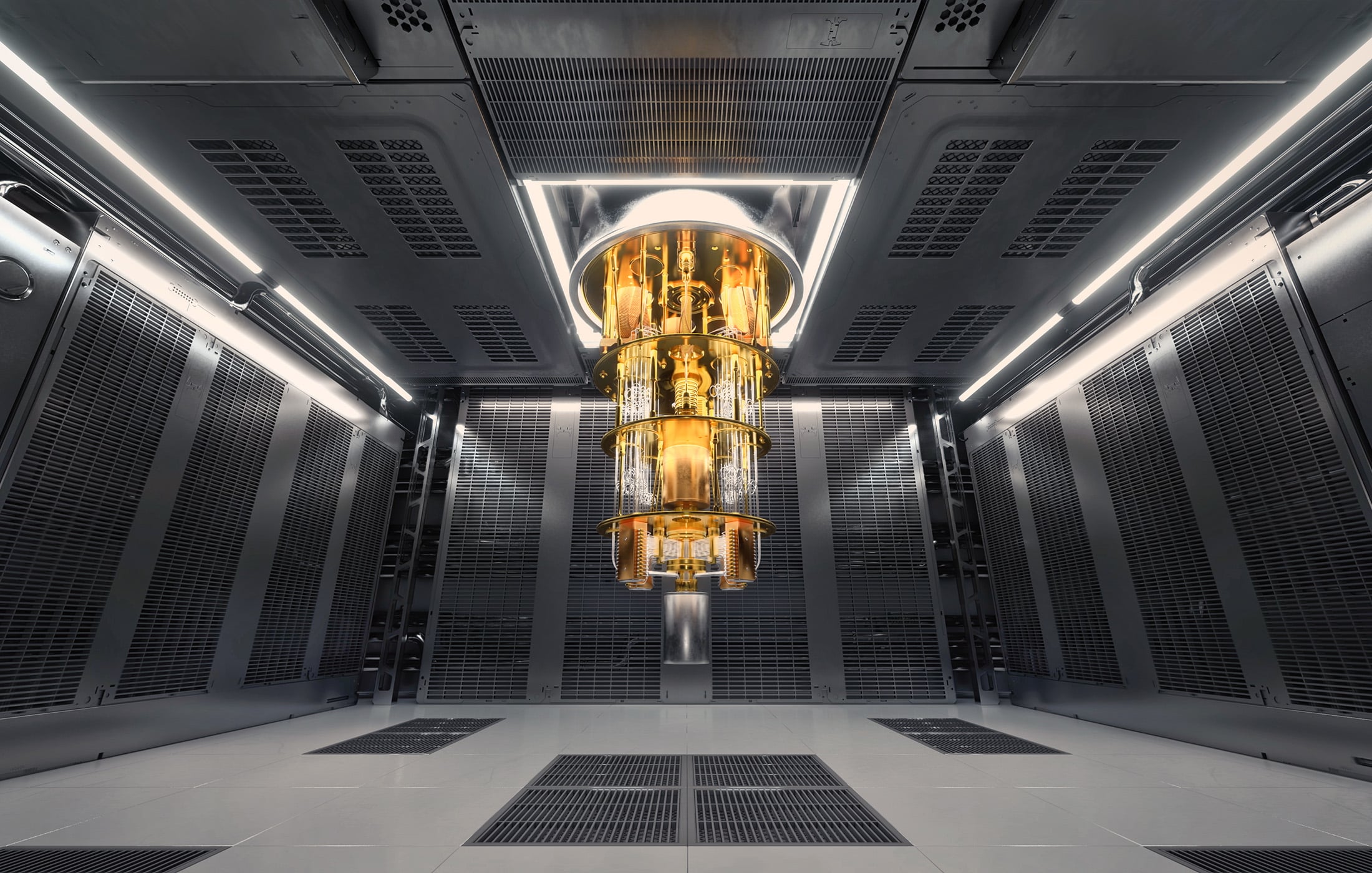
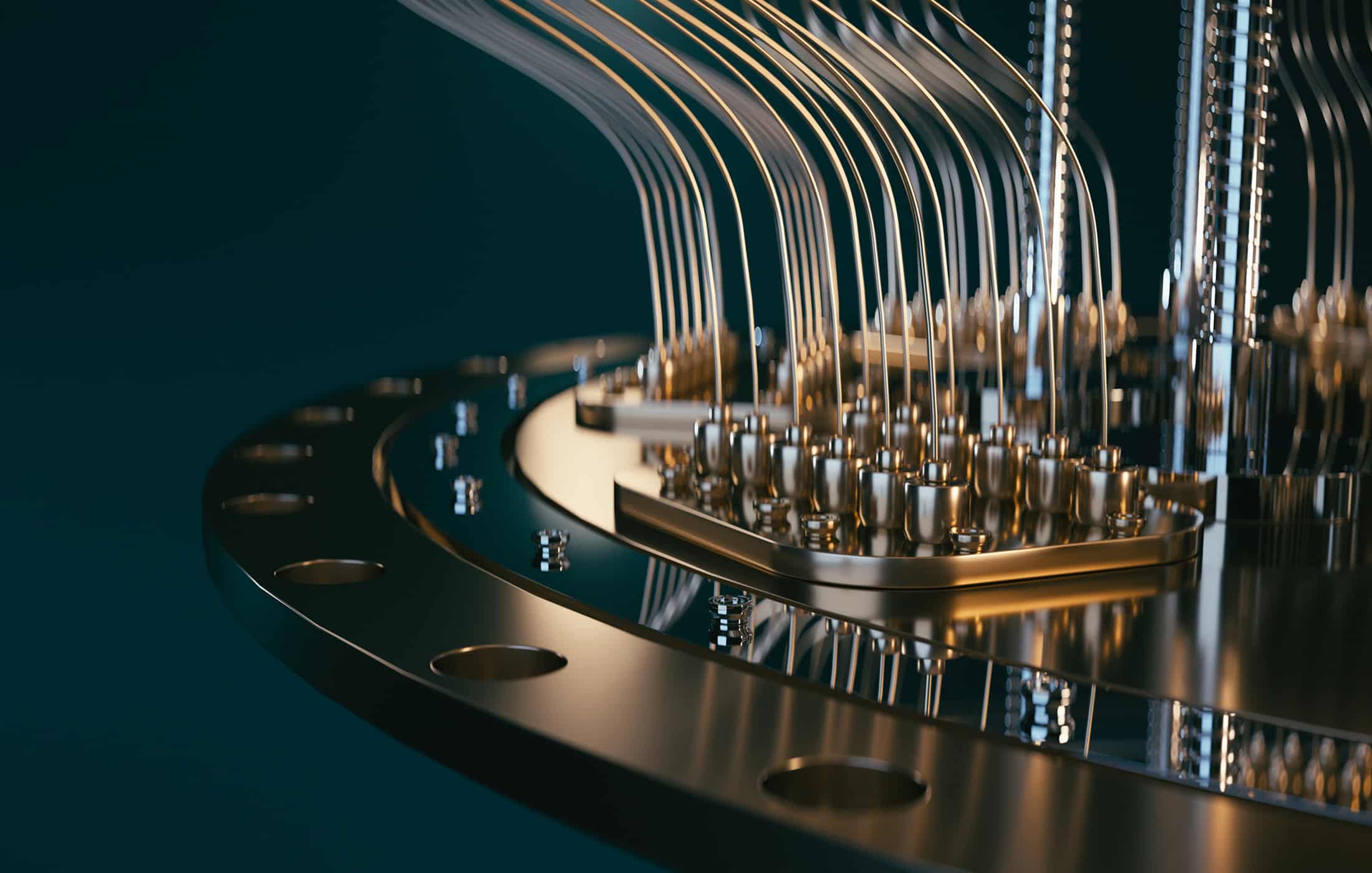
Quantum Computing Modalities: Acoustic (Phononic) Quantum Systems
(For other quantum computing modalities and architectures, see Taxonomy of…
Fidelity in Quantum Computing
Introduction According to a recent MIT article, IBM aims to build a 100,000…
Quantum Technology Use Cases in Supply Chain & Logistics
Introduction Quantum computing is poised to be a game-changer for…
Harvest Now, Decrypt Later (HNDL) Risk
Introduction In the world of cybersecurity, there’s a ticking time bomb that…
Post-Quantum Cryptography PQC Challenges
Introduction As the quantum threat approaches, the need to prepare our…
Understanding and Addressing Biases in Machine Learning
Introduction ML enables computers to learn from data and make decisions,…