Mapping Your Quantum Technology Dependencies — Before They Become Vulnerabilities
Every organisation and nation deploying quantum technology depends on foreign suppliers, platforms, standards, and talent. Some of those dependencies are routine. Others are strategic vulnerabilities — points where a geopolitical shift, an export control change, or a vendor decision could disrupt your quantum capability overnight. Our Quantum Sovereignty Assessment systematically maps those dependencies across your entire quantum technology stack, rates their severity and replaceability, and delivers a clear set of actions to build sovereign optionality where it matters.
Our Expertise
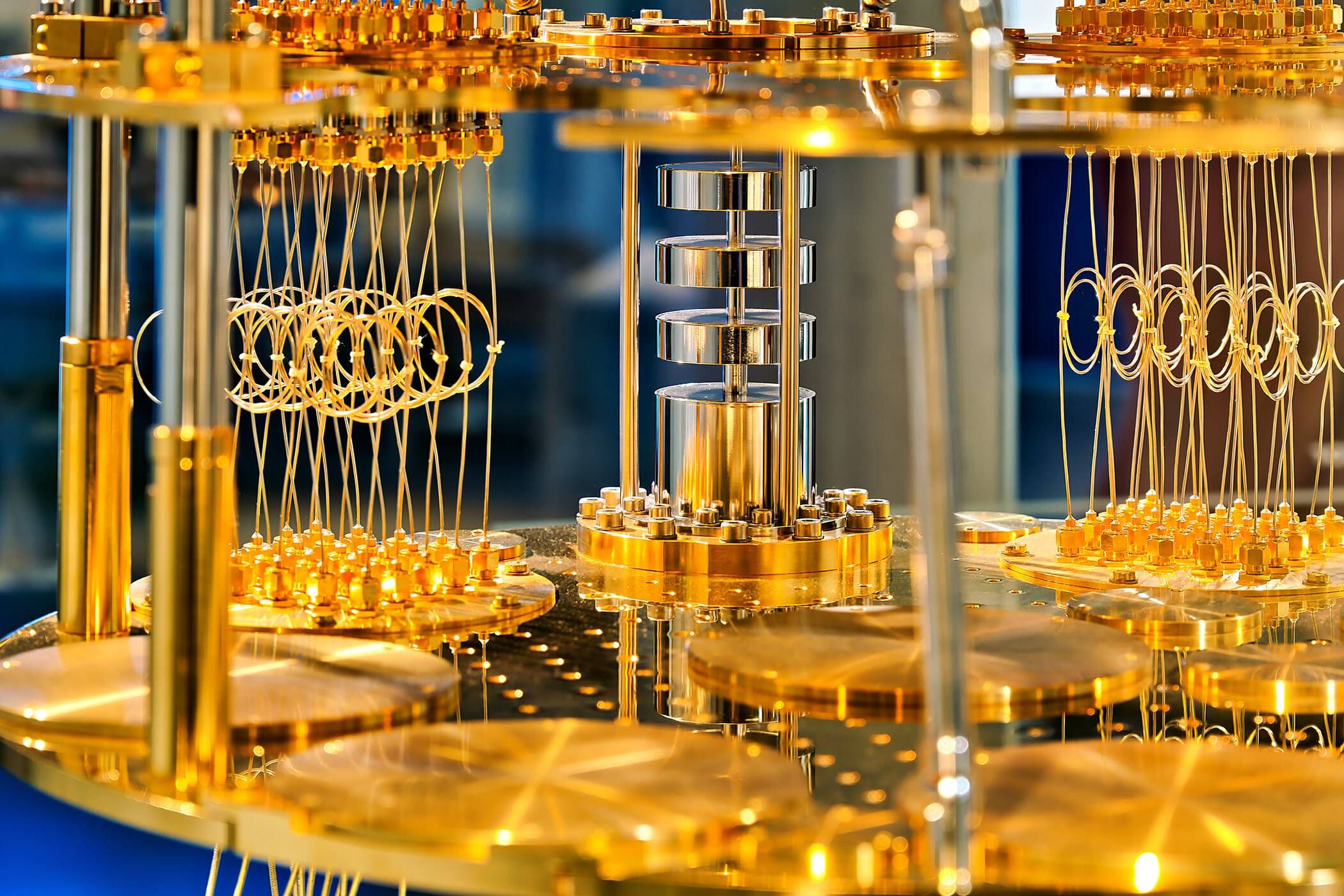
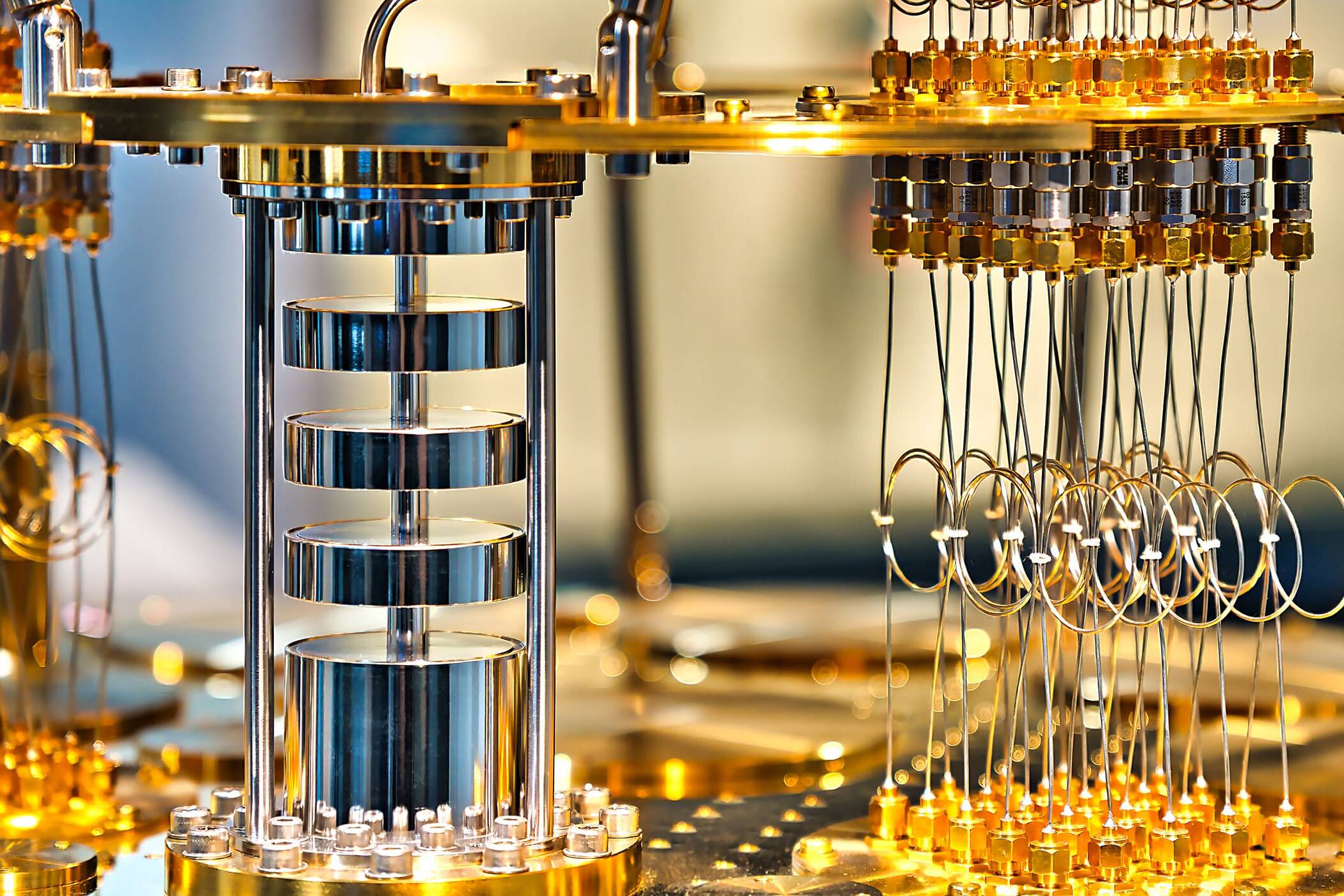
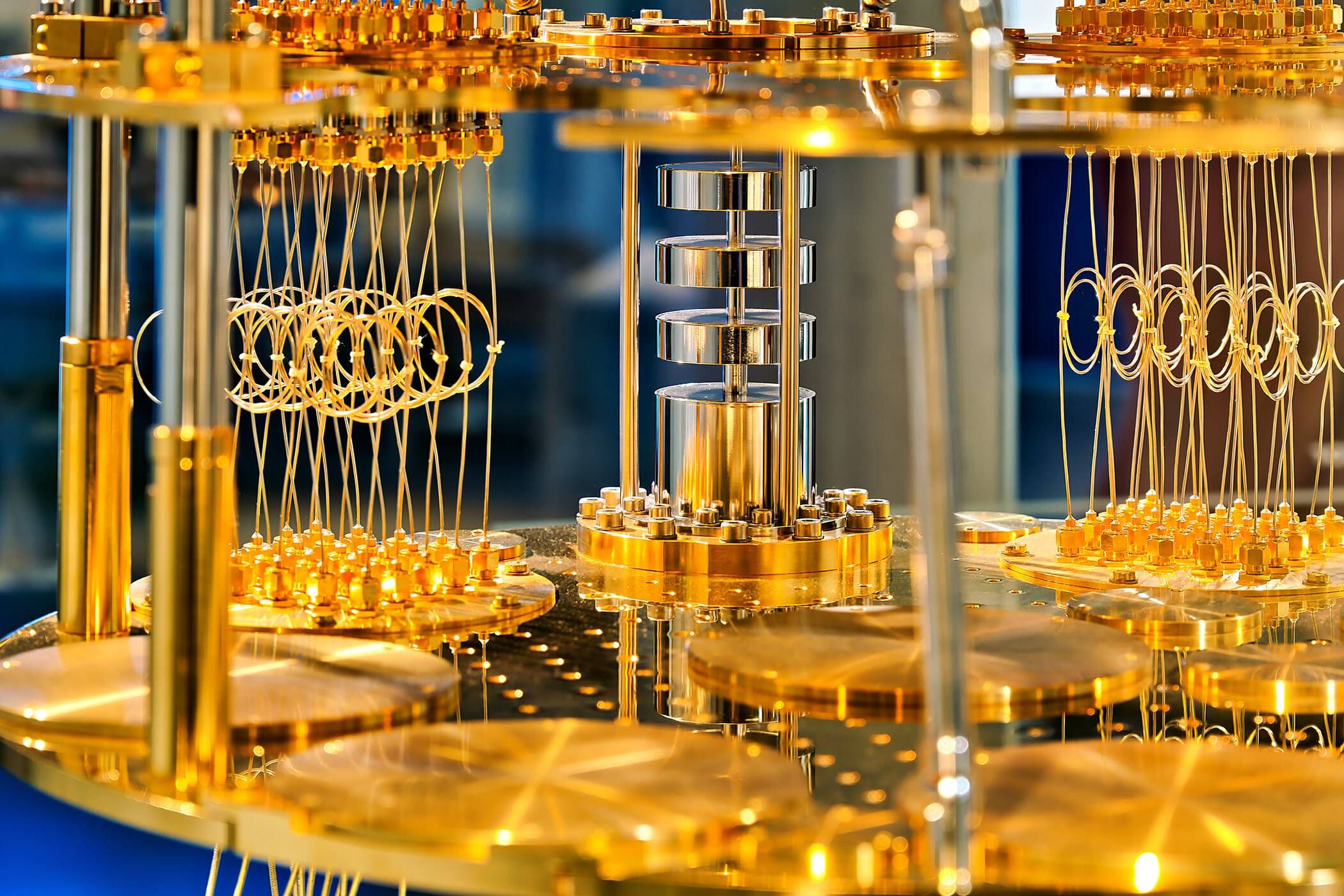
Applied Quantum brings a rare combination of capabilities to sovereignty assessment work. As a quantum systems integrator that builds quantum computers from open-architecture components, we understand the quantum supply chain at a level of detail that strategy consultancies and policy shops cannot match. We know which QPU vendors ship to which countries, which control electronics have export restrictions, which middleware components have foreign dependencies buried three layers deep, and where the real single points of failure sit. We combine this technical depth with extensive experience in quantum security, national quantum strategy, and geopolitical technology risk.
Our sovereignty assessment methodology is grounded in the principle of sovereign optionality — the idea that the goal is not autarky (building everything domestically) but rather maintaining the ability to pivot, switch suppliers, or bring capability in-house if circumstances demand it. Total self-sufficiency in quantum technology is neither achievable nor desirable for most countries. What is achievable — and essential — is ensuring that no single foreign actor can shut down your quantum programme with a phone call.
What We Assess
We conduct a systematic, layer-by-layer analysis of your quantum technology dependencies. The assessment covers every part of the stack where a foreign dependency could create strategic exposure:
- Hardware sourcing: Where do your QPUs come from? Your control electronics? Your cryogenic systems? What are the export control regimes governing each component? Who are the alternative suppliers, and how quickly could you switch
- Software and middleware: Which SDKs, compilers, firmware, and middleware layers does your quantum platform depend on? Are they open-source, proprietary, or a mix? Who maintains them, and under which jurisdiction? Could access be revoked
- Cloud and infrastructure: If you use cloud-based quantum services, what happens if access is withdrawn? Do you have on-premises alternatives? What data crosses international boundaries
- Standards and protocols: Which cryptographic, networking, and interoperability standards does your quantum infrastructure rely on? Are those standards at risk of geopolitical bifurcation?
- Talent: Where are your quantum engineers, physicists, and researchers from? What are the visa, export control, and security clearance implications? How concentrated is your expertise in a small number of individuals or institutions?
- Investment and IP: Who owns equity in your quantum technology suppliers? Are there foreign investors with influence or control rights? Where does your quantum IP reside, and under which legal jurisdiction?





The Sovereign Optionality Framework
We do not assess sovereignty against a standard of total self-sufficiency — that would produce an impractical wish list. Instead, we use the sovereign optionality framework, which asks a different question for each dependency: if this supplier, platform, or capability became unavailable tomorrow, what are your options?
For each dependency we identify, we evaluate:
- Severity: What is the operational impact if this dependency is disrupted? Does your quantum programme stop, degrade, or continue with workarounds?
- Replaceability: Are there alternative suppliers, open-source equivalents, or domestic capabilities that could substitute? How quickly, and at what cost?
- Geopolitical exposure: Is this dependency concentrated in a jurisdiction where political, trade, or regulatory action could disrupt access? What is the trajectory of risk — stable, increasing, or volatile?
- Control posture: Do you have contractual, technical, or legal protections that mitigate the dependency? Source code escrow, multi-vendor architectures, stockpiled spares, knowledge transfer agreements?
The result is not a binary “sovereign / not sovereign” verdict. It is a nuanced map showing where you have adequate optionality, where you have acceptable risk, and where you have unacceptable single points of failure that require action.
What We Deliver
The assessment produces a set of concrete, actionable outputs:
- Quantum technology dependency map: A structured view of every significant dependency across your quantum stack, organised by layer (hardware, software, cloud, standards, talent, investment) and rated by severity, replaceability, and geopolitical exposure.
- Sovereign optionality report: For each high-severity dependency, an analysis of what alternative sources exist, what domestic or allied capabilities could be developed, what procurement or architectural changes would reduce exposure, and what the estimated cost and timeline of each mitigation would be.
- Prioritised action plan: A ranked list of recommended actions — from quick wins (diversifying a single-source component) to strategic investments (building domestic systems integration capability) — with ownership, budget estimates, and sequencing.
- Ongoing monitoring framework: A set of leading indicators and trigger points to monitor, so that emerging sovereignty risks are detected before they become crises. This includes geopolitical developments, vendor M&A activity, standards evolution, and export control changes.




How It Connects to Our Other Services
The Sovereignty Assessment is often the starting point for a broader engagement:
- The findings feed directly into our Sovereignty Stress Test exercises, which put the identified dependencies under pressure through scenario-based tabletop simulations.
- Where the assessment identifies a need for sovereign quantum computing infrastructure, our Quantum Systems Integration practice can build it — assembling quantum computers from open-architecture components under the client’s control.
- Where software and middleware dependencies are identified as high-risk, our Quantum OS, Middleware & Integration Layer Development practice can build sovereign alternatives.
- Where the assessment informs national strategy decisions, our National & Sector Quantum Strategy service provides the policy and industrial strategy advisory to act on the findings.
Who This Is For
This service is designed for organisations where quantum technology dependencies carry genuine strategic weight:
- Government ministries responsible for science, defence, industry, or digital policy
- National cyber security agencies and critical infrastructure regulators
- Defence and intelligence organisations deploying or planning quantum capability
- Sovereign wealth funds and state investment bodies evaluating quantum technology portfolios
- Critical infrastructure operators (energy, finance, telecoms, transport) with quantum exposure
- Defence contractors and technology companies operating in sensitive supply chains


Your quantum technology stack has dependencies you haven't mapped, in jurisdictions you may not have considered, with concentration risks that only become visible under pressure. We find them before your adversaries exploit them. Contact us to discuss a Quantum Sovereignty Assessment for your organisation or programme.
- Inquire about our services
- Request detailed analyst reports
- Learn about our educational programs
- Discuss partnership opportunities
- Explore our R&D collaboration
- Get support for your quantum security
- Request a demo of our solutions